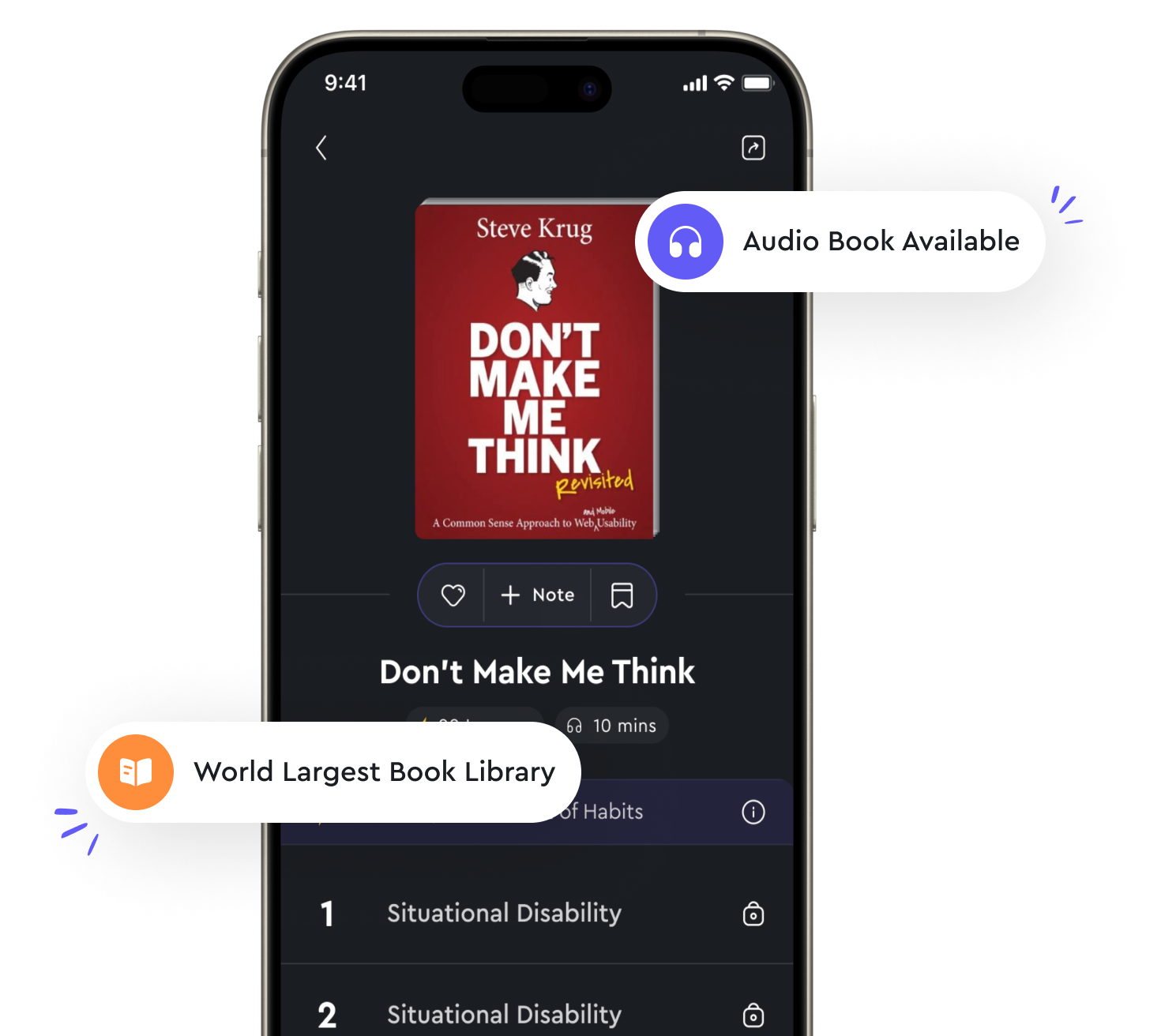
Audio available in app
Software development security is essential for secure applications from "summary" of Official (ISC)2 Guide to the CISSP CBK by Adam Gordon
Software development security is a critical component of building secure applications. When developing software, security should be incorporated throughout the entire development lifecycle, from the initial design phase to deployment and maintenance. By integrating security into each stage of the software development process, potential vulnerabilities can be identified and addressed early on, reducing the risk of security breaches and threats. One of the key reasons why software development security is essential for secure applications is that vulnerabilities in software can be exploited by malicious actors to gain unauthorized access to sensitive information or disrupt critical systems. By implementing security best practices during the development process, such as secure coding practices, regular security testing, and code reviews, developers can minimize the likelihood of these vulnerabilities being exploited. Furthermore, incorporating security into the software development process can help organizations comply with various regulatory requirements and industry standards related to data protection and privacy. For example, many regulations, such as the General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA), require organizations to implement security measures to protect sensitive data. By building security into their applications from the start, organizations can demonstrate compliance with these regulations and avoid potential fines and penalties. In addition to protecting sensitive data and complying with regulations, software development security can also help organizations build trust with their customers and stakeholders. In today's digital age, consumers are increasingly concerned about the security of their personal information, and a data breach can have serious consequences for an organization's reputation and bottom line. By prioritizing security in the software development process, organizations can demonstrate their commitment to protecting customer data and maintaining a secure environment for their users.- Software development security is essential for building secure applications that protect sensitive data, comply with regulations, and build trust with customers. By integrating security into the software development lifecycle, organizations can mitigate the risk of security breaches and ensure that their applications are resilient to cyber threats.
Similar Posts
Behavioral design focuses on system functionality
When designing a system, it is crucial to focus on the behavior of the system in order to ensure its functionality. Behavioral ...
Understanding Java is key to developing Android apps
To become a successful Android app developer, you need to have a solid understanding of Java. Why? Because Java is the primary ...
Evolution of Bitcoin technology
Bitcoin technology has undergone significant evolution since its inception in 2009. The first version of Bitcoin was released b...
DHCP assigns IP addresses automatically
When setting up a network, one of the most important tasks is assigning IP addresses to all the devices that will be connected....
The system is broken
When we say "the system is broken," what we really mean is that the current state of affairs is not working as it should. The s...
Data visualization aids in understanding
Data visualization is a powerful tool that can help individuals make sense of complex data. By presenting information in a visu...
Society must work together to harness the potential of the Fourth Industrial Revolution for the benefit of all
The Fourth Industrial Revolution presents a vast array of opportunities for humanity. From artificial intelligence to biotechno...