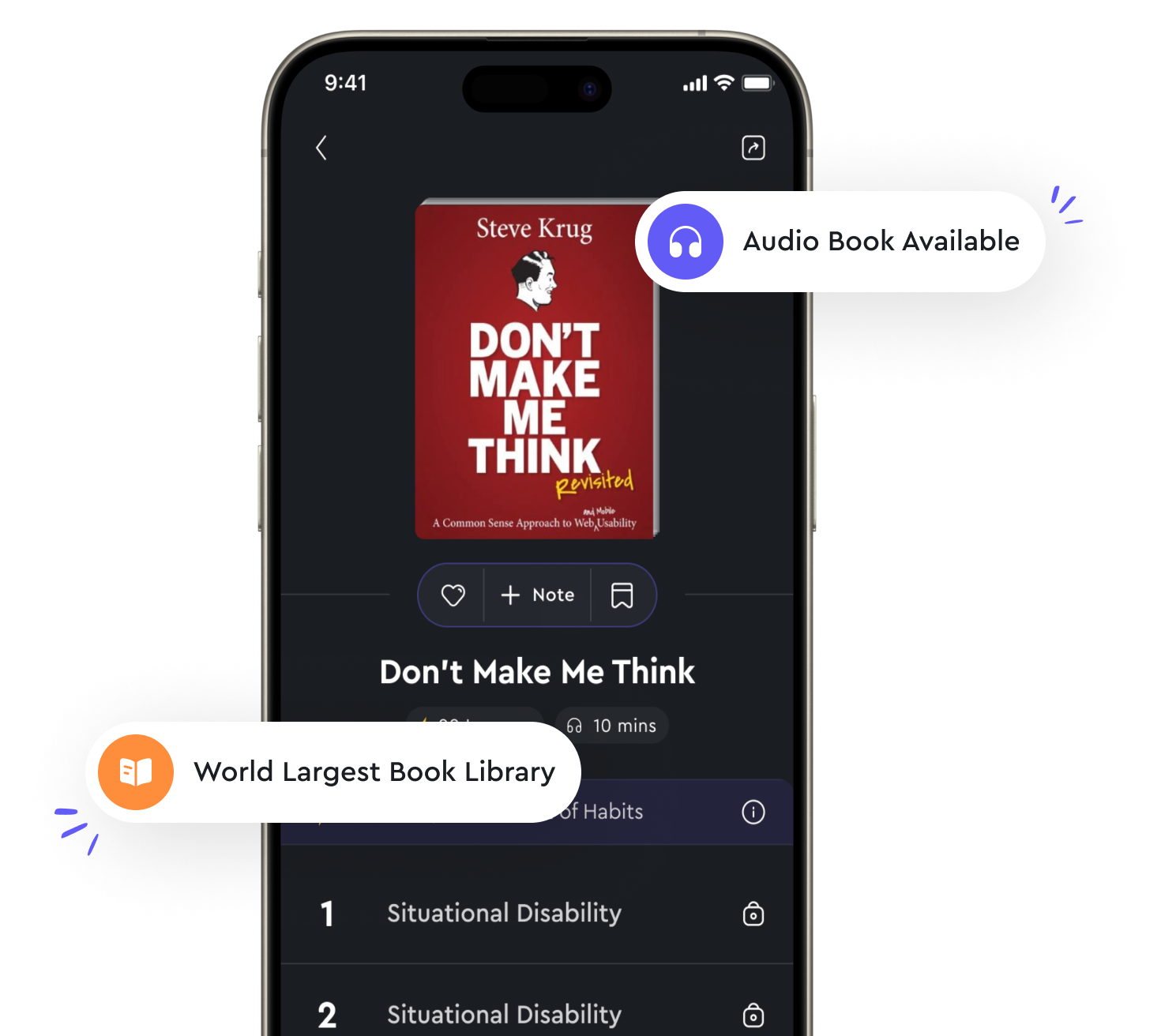
Audio available in app
Communication and network security are significant areas from "summary" of Official (ISC)2 Guide to the CISSP CBK by Adam Gordon
Communication and network security are foundational elements in the world of information security. As organizations rely more heavily on interconnected systems and networks to conduct their operations, the need to protect the confidentiality, integrity, and availability of data and resources becomes increasingly critical. Effective communication security measures are essential to ensure that sensitive information is safeguarded from unauthorized access or disclosure. This includes encryption, access controls, and secure communication protocols to protect data while it is in transit. By implementing strong authentication mechanisms and encryption algorithms, organizations can prevent eavesdropping and data tampering during communication exchanges. Network security, on the other hand, focuses on the protection of the underlying infrastructure that supports communication activities. This includes securing network devices, such as routers, switches, and firewalls, as well as monitoring network traffic for signs of malicious activity. By implementing intrusion detection and prevention systems, organizations can quickly identify and respond to potential security threats that may compromise the integrity of the network. Additionally, network security measures also encompass securing wireless networks, which are increasingly common in today's mobile-centric world. Organizations must take steps to secure their wireless networks by implementing strong authentication mechanisms, encryption protocols, and monitoring tools to detect unauthorized access attempts.- Communication and network security are significant areas that require careful planning, implementation, and monitoring to ensure the ongoing protection of an organization's information assets. By addressing these critical areas effectively, organizations can mitigate the risks associated with unauthorized access, data breaches, and network disruptions, thereby safeguarding their reputation, financial stability, and competitive advantage in the marketplace.